- Home
- Customized Toolkit
Customized Toolkit
Our proprietary security toolkit combines multiple specialized tools developed through years of security research. From firmware analysis to protocol fuzzing and vulnerability detection, our suite provides comprehensive security assessment capabilities across embedded systems, automotive platforms, and connected environments.
Our toolkit

Firmware Security Scanner
Comprehensive binary analysis tool that identifies vulnerabilities, outdated components, weak configurations, and hidden risks inside firmware images. Includes integrated SBOM analysis to map software composition, detect known vulnerabilities (CVE mapping), assess licensing risks, and track supply chain dependencies—all through automated reverse engineering and pattern matching.
Automotive Protocol Fuzzers
Specialized fuzzing tools for automotive and IoT communication protocols including CAN, Automotive Ethernet, FlexRay, UDS, and wireless interfaces. Discover memory corruption vulnerabilities, protocol implementation flaws, and edge-case behaviors that traditional testing misses.


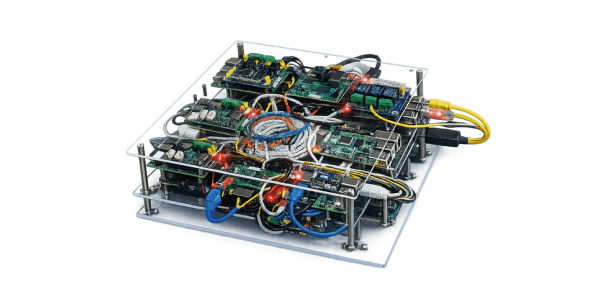
CyberStand - Automated Testing Platform
Integrated testing environment for systematic security validation with flexible deployment options. Combines automated scanning, manual testing workflows, hardware-in-the-loop (HIL) support, and comprehensive reporting capabilities. Supports both on-site and remote testing configurations, enabling distributed teams to conduct security assessments without physical access to test benches—ideal for multi-location development and supplier coordination.
Deployment options
Our Services Using Our Tools
We deploy our toolkit in penetration testing engagements, security assessments, and vulnerability research projects—continuously refining capabilities based on real-world findings.
Client-Deployed Solutions Make our tools available to your internal teams with customization options including
- Platform-specific scanning configurations for your ECU variants
- Custom fuzzing strategies tailored to your protocol implementations
- OEM-specific compliance rule sets and reporting templates
- Integration with your existing development and testing infrastructure
- Training and knowledge transfer for your security teams
Why choose our toolkit
Proven in Real Operations
Tools we actively use in our own penetration testing and research—not shelf-ware. Continuously improved based on vulnerabilities discovered in production systems.
Efficiency & Scale
Automation-supported workflows reduce analysis time from weeks to hours while maintaining comprehensive coverage across multiple programs simultaneously.
Purpose-Built for Complex Systems
Specifically designed for firmware-heavy systems, protocol-level testing, distributed testing environments, and multi-supplier coordination common in automotive, industrial, and embedded sectors.
