- Home
- Penetration Testing Service
Penetration Testing Service
We identify real-world security weaknesses across embedded, cloud, and connected systems through advanced penetration testing backed by proprietary research. Our approach uncovers zero-day vulnerabilities and provides clear, actionable insights that help you strengthen your products and reduce cyber risks to enhance your security posture.
What we test
Automotive & Industrial Systems
ECU penetration testing
CAN/Automotive Ethernet attack simulation
OTA update system security
Wireless interface testing (Bluetooth, WiFi, UWB, RF)
KeyFob and PKES (Passive Keyless Entry) security
Industrial control system (ICS) security
Vehicle architecture security assessment


Cloud & Enterprise Infrastructure
Identity and Access Management (IAM)
API and backend service testing
Container and orchestration security
Multi-cloud environment assessment
Enterprise application security
Configuration and infrastructure validation
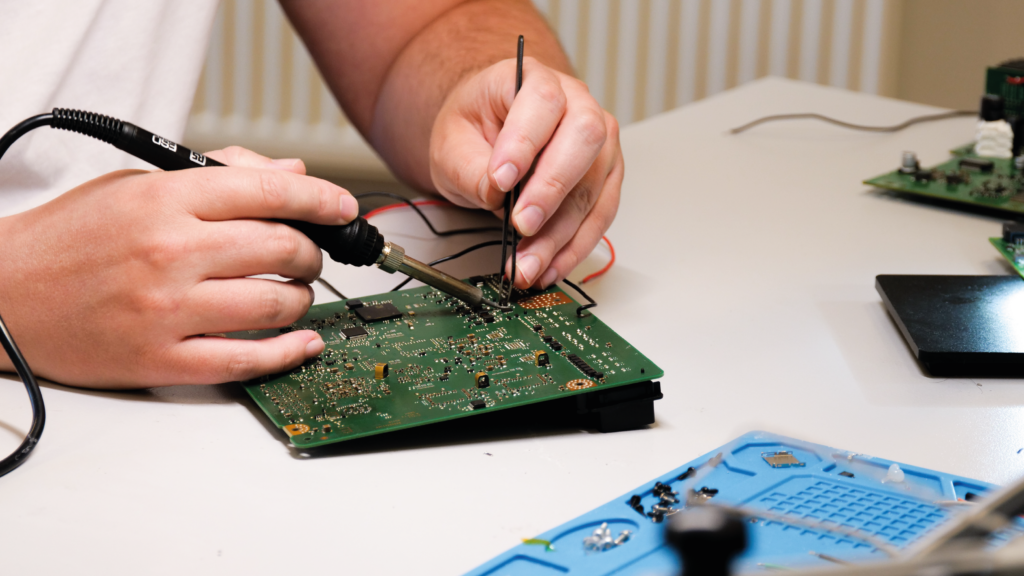
Embedded Systems & Hardware
Hardware security analysis
Firmware reverse engineering
Bootloader and secure boot validation
Communication protocol testing
Smart device security assessment
Interface and peripheral analysis
How We Test
Our systematic approach combines advanced automation with deep manual expertise to uncover vulnerabilities that automated scanners miss
Planning & Threat Modelling
Define scope, understand system architecture, map attack surfaces, and identify potential threat vectors based on your specific deployment context and threat landscape.
Static & Dynamic Analysis
Conduct binary analysis, firmware extraction, configuration review, and runtime behavior assessment to identify initial weaknesses and security control gaps.
Manual Exploitation & Research
Perform targeted adversarial testing using proprietary tools and zero-day research capabilities. Chain vulnerabilities to demonstrate real-world attack scenarios and validate exploitability.
Impact Assessment
Analyze findings to determine severity, business impact, exploitability factors, and potential system-wide or cross-component effects.
Reporting & Remediation Verification
Deliver detailed, risk-ranked reports with evidence-backed findings and practical remediation guidance. Provide retesting to confirm effective fixes.
Why Choose Us
Research-Driven Expertise
Leverage proprietary zero-day research capabilities and extensive penetration testing experience. We don't just run tools, we discover new attack vectors and develop custom exploits.
Compliance-Ready
Structured, traceable, and thoroughly documented testing practices aligned with regulatory requirements. Our reports integrate seamlessly into your compliance and certification workflow.
Automotive & Industrial Specialization
Deep expertise in automotive and industrial security standards (ISO/SAE 21434, UN R155/R156), embedded systems, automotive protocols, and safety-critical system testing across major OEMs and tier-1 suppliers.
